Unlocking the Potential of RBC Crypto
In the dynamic realm of digital finance, RBC Crypto emerges as a promising contender, poised to redefine the landscape of transactions and investments. Let’s delve into the depths of RBC Crypto, exploring its features, applications, and potential impact on the financial ecosystem.
Introduction to RBC Crypto: A New Frontier
RBC Crypto, short for “Royal Bank of Canada Crypto,” represents the banking giant’s foray into the world of digital assets and blockchain technology. With its roots firmly planted in traditional finance, RBC Crypto aims to bridge the gap between traditional banking and the burgeoning digital economy.
Understanding the Mechanics of RBC Crypto
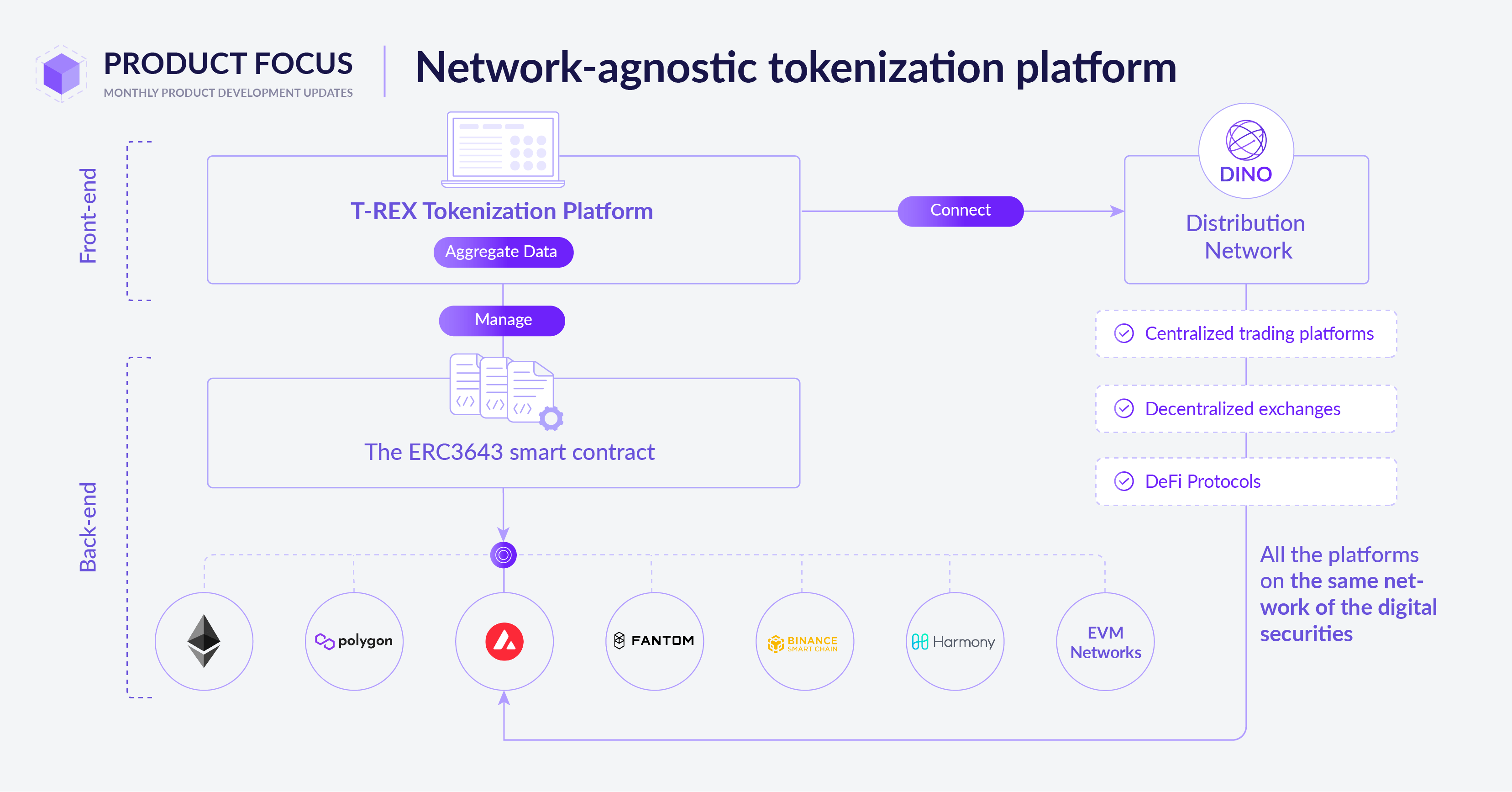
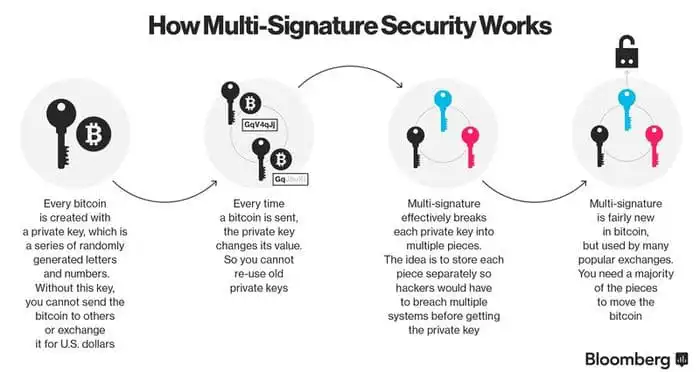
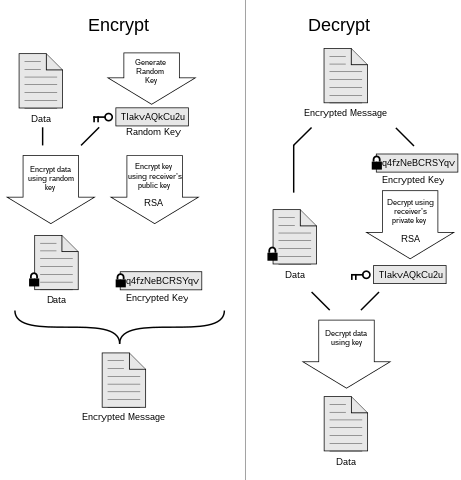
At its core, RBC Crypto operates on blockchain technology, a decentralized ledger system that ensures the security and transparency of transactions. Unlike traditional banking systems, which rely on centralized authorities, RBC Crypto leverages blockchain’s distributed architecture to enable peer-to-peer transactions without the need for intermediaries.
The Advantages of RBC Crypto: Efficiency and Security
One of the key advantages of RBC Crypto is its ability to streamline transactions, reducing the time and costs associated with traditional banking processes. By eliminating intermediaries and automating processes through smart contracts, RBC Crypto offers a more efficient and cost-effective alternative to traditional banking.
RBC Crypto Applications: From Payments to Investments
Beyond basic transactions, RBC Crypto has a wide range of applications across various sectors. From cross-border payments to supply chain management, RBC Crypto can facilitate secure and transparent transactions in a variety of industries. Additionally, RBC Crypto opens up new avenues for investment, allowing individuals and institutions to diversify their portfolios with digital assets.
Regulatory Considerations and Compliance
Despite its potential, RBC Crypto operates within the framework of existing regulatory guidelines and compliance standards. As a regulated financial institution, RBC must ensure that its crypto offerings comply with anti-money laundering (AML) and know your customer (KYC) regulations to prevent illicit activities and protect customer assets.
Challenges and Opportunities for RBC Crypto
While RBC Crypto holds immense promise, it also faces challenges on its path to widespread adoption. Scalability, interoperability, and regulatory uncertainty are among the key hurdles that must be addressed. However, with ongoing development and collaboration within the blockchain community, RBC Crypto is well-positioned to overcome these challenges and emerge as a leading player in the digital finance space.
The Future of Finance with RBC Crypto
As the financial landscape continues to evolve, RBC Crypto stands at the forefront of innovation, driving forward the adoption of blockchain technology in traditional finance. With its focus on efficiency, security, and transparency, RBC Crypto has the potential to revolutionize the way we transact and interact in the digital age, paving the way for a more inclusive and accessible financial ecosystem. Read more about rbc crypto