Securing Token Transfer: Enhancing Digital Transaction Safety
The secure transfer of tokens is a critical aspect of modern digital transactions, ensuring the integrity and confidentiality of sensitive information. This article explores the significance of secure token transfer, the mechanisms involved, and its role in fortifying the safety of digital transactions.
The Importance of Secure Token Transfer
Secure token transfer is paramount in safeguarding digital transactions. Tokens, whether representing currency, access rights, or other sensitive data, require a secure transfer mechanism to prevent unauthorized access or tampering. This process is foundational in maintaining the trust and reliability of digital transactions.
Mechanisms for Secure Token Transfer
Various mechanisms contribute to the secure transfer of tokens. Encryption plays a central role, ensuring that tokens are transmitted in a format that is indecipherable to unauthorized entities. Secure communication protocols, such as HTTPS, add an extra layer of protection, guaranteeing the confidentiality of token transfers.
Tokenization in Financial Transactions
In financial transactions, secure token transfer is prevalent through tokenization. Instead of transmitting sensitive card details, a token representing the payment information is used. This minimizes the risk associated with exposing financial data during transactions, enhancing the overall security of electronic payments.
Blockchain Technology and Token Security
Blockchain technology has revolutionized token transfer by providing a decentralized and tamper-resistant ledger. Tokens on a blockchain are securely transferred through consensus mechanisms, ensuring that transactions are valid and irreversible. This technology adds transparency and immutability to the token transfer process.
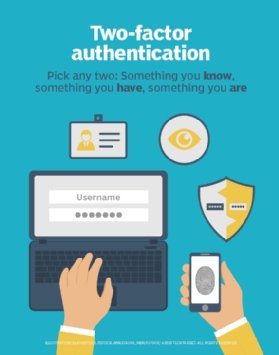
Multi-Factor Authentication for Token Authorization
Secure token transfer often involves multi-factor authentication (MFA) to ensure that the entity initiating the transfer is authorized. MFA combines multiple authentication factors, such as passwords, biometrics, and secure tokens, adding layers of security to the authorization process and preventing unauthorized token transfers.
Secure Token Transfer in Mobile Applications
Mobile applications frequently rely on secure token transfer for various functions, from in-app purchases to authentication. Mobile platforms implement secure communication channels and tokenization techniques to protect sensitive data during transactions, contributing to a secure mobile user experience.
Securing Token Transfer Across Networks
Tokens often traverse networks during transfers, making network security paramount. Employing virtual private networks (VPNs) or secure communication protocols ensures that token data remains encrypted and protected from interception during transit. This is particularly crucial in scenarios involving remote transactions or cloud-based services.
Token Lifecycle Management and Security
Managing the entire lifecycle of tokens is essential for security. From issuance to revocation, a robust token management system ensures that only valid tokens are in circulation. Regular audits, monitoring, and updates to encryption protocols contribute to maintaining the security of token transfers.
Challenges and Mitigations in Token Transfer Security
While secure token transfer is fundamental, challenges exist. Mitigating the risk of man-in-the-middle attacks, ensuring endpoint security, and addressing vulnerabilities in the token transfer process require continuous vigilance. Implementing security best practices and staying abreast of emerging threats are crucial for overcoming these challenges.
Explore Secure Token Transfer at www.itcertswin.com
For a deeper understanding of secure token transfer, its mechanisms, applications, and best



