Secure Your Connections with Robust TLS Technology
In today’s digital landscape, ensuring the security of data transmission over the internet is paramount. One crucial technology that plays a pivotal role in this aspect is Transport Layer Security (TLS). Let’s delve into the significance and implementation of TLS to understand how it fortifies the security of your online communications.
Understanding Transport Layer Security (TLS)
Transport Layer Security, commonly known as TLS, is a cryptographic protocol designed to secure communication over a computer network. It operates at the transport layer and ensures the privacy and integrity of data exchanged between applications. TLS has become the successor to the earlier Secure Sockets Layer (SSL) protocol, offering enhanced security features and improved algorithms.
Encryption for Data Confidentiality
One of the primary functions of TLS is to provide encryption for data transmitted between a client and a server. This encryption ensures the confidentiality of sensitive information, making it extremely challenging for unauthorized entities to intercept and decipher the data. Through robust encryption algorithms, TLS safeguards your personal and financial data during online transactions and interactions.
Authentication with SSL Certificates
TLS enhances security not only through encryption but also by implementing a robust system of authentication. SSL certificates play a crucial role in this process, verifying the identity of websites and ensuring that users are connecting to legitimate and trustworthy servers. This authentication mechanism prevents man-in-the-middle attacks and assures users of the reliability of the online services they are accessing.
Securing Sensitive Information on the Web
In an era where online transactions and data exchange are ubiquitous, TLS is indispensable for securing sensitive information on the web. Whether you’re logging into your online banking account, making an e-commerce purchase, or accessing confidential work-related data, TLS creates a secure tunnel that shields your data from prying eyes.
TLS and Website Security
For website owners and administrators, implementing TLS is a fundamental step in enhancing overall website security. Not only does it protect user data, but it also contributes to building trust among visitors. Modern web browsers often display a padlock icon or other indicators to signify a secure TLS connection, reassuring users that their data is safe on the website.
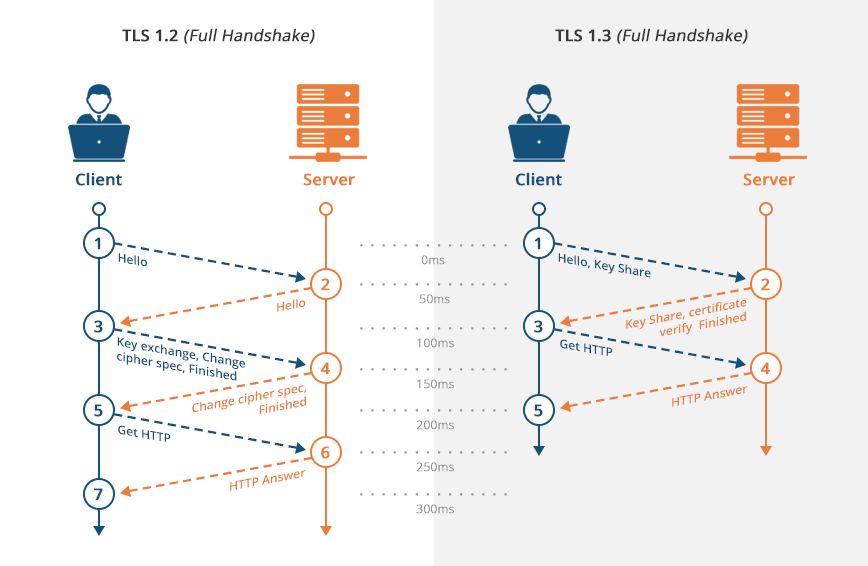
Upgrading to the Latest TLS Versions
As with any technology, keeping abreast of the latest developments and versions is crucial for maintaining optimal security. It is recommended to use the latest TLS versions to benefit from improved algorithms and security features. Regular updates ensure that your systems are equipped to counter emerging threats and vulnerabilities.
Integrating TLS for Comprehensive Network Security
Beyond securing individual communications, TLS contributes to comprehensive network security. By encrypting data at the transport layer, it protects against various cyber threats, including eavesdropping, data tampering, and unauthorized access. The integration of TLS into network protocols strengthens the overall resilience of digital communications.
TLS and Compliance with Data Protection Regulations
In an era of heightened awareness regarding data privacy, TLS plays a significant role in ensuring compliance with data protection regulations. Many regulatory frameworks, such

