Empowering Tech Education with Simplilearn Blockchain
Introduction: Redefining Learning in the Digital Age
Simplilearn Blockchain is at the forefront of revolutionizing tech education, providing learners worldwide with access to cutting-edge knowledge and skills. In this article, we explore how Simplilearn’s innovative approach to blockchain education is reshaping the landscape of digital learning.
The Rise of Simplilearn Blockchain: A Beacon of Digital Transformation
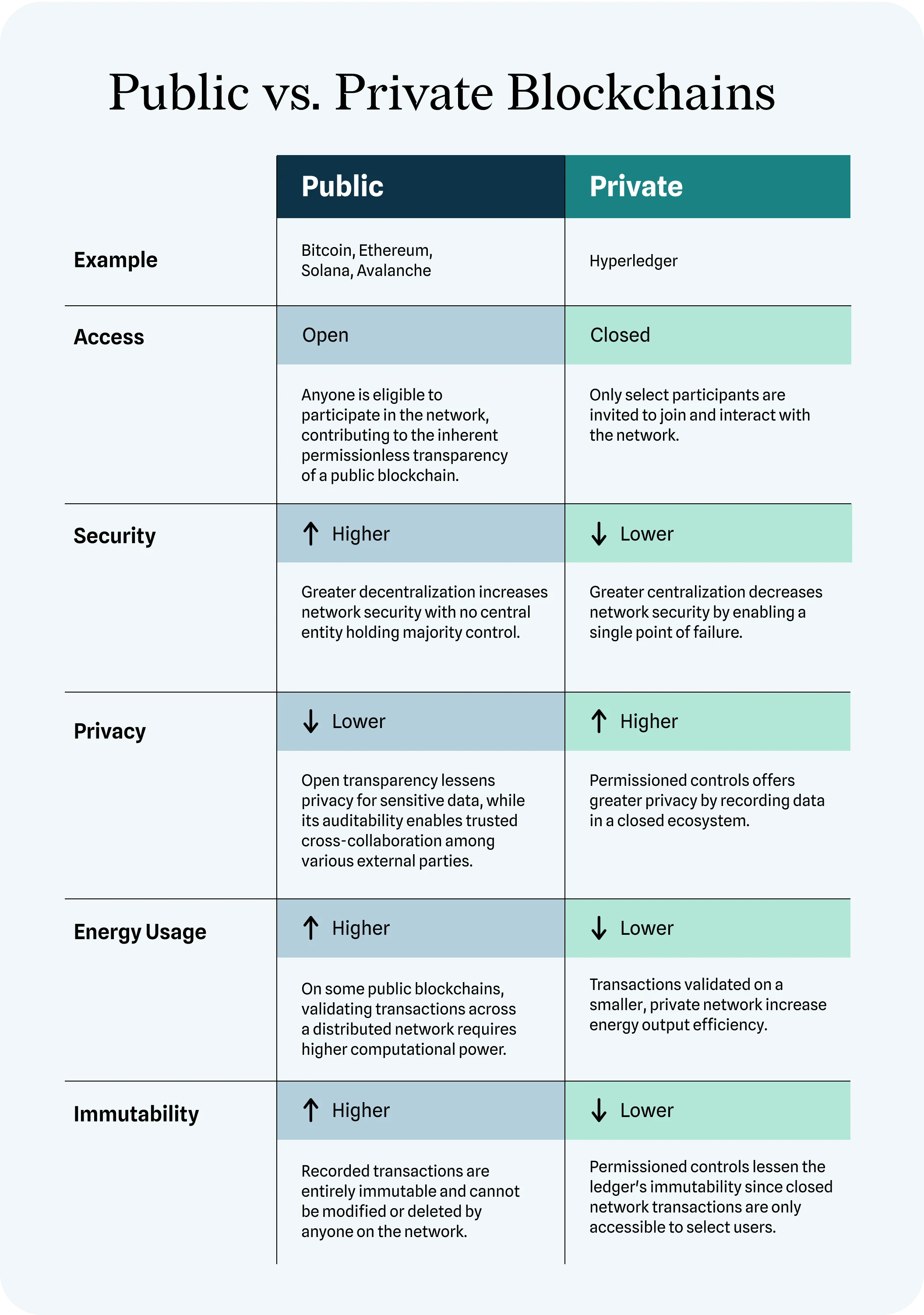
In an era dominated by rapid technological advancements, staying ahead of the curve is essential. Simplilearn Blockchain offers a comprehensive curriculum designed to equip learners with the knowledge and expertise needed to thrive in today’s digital economy. From foundational concepts to advanced applications, Simplilearn covers all aspects of blockchain technology, empowering individuals to navigate the complexities of the digital world.
Breaking Down Complex Concepts: Simplilearn’s Pedagogical Approach
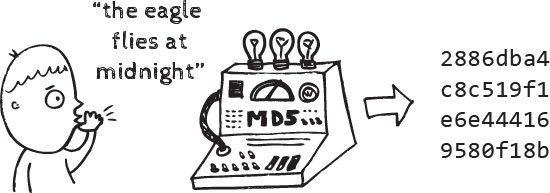
At the heart of Simplilearn’s success is its commitment to making complex concepts accessible and understandable. Through a combination of interactive modules, hands-on projects, and expert-led instruction, Simplilearn demystifies blockchain technology, allowing learners to grasp even the most intricate concepts with ease. Whether you’re a beginner or an experienced professional, Simplilearn’s user-friendly platform ensures a seamless learning experience for all.
Real-world Applications: Bridging Theory and Practice
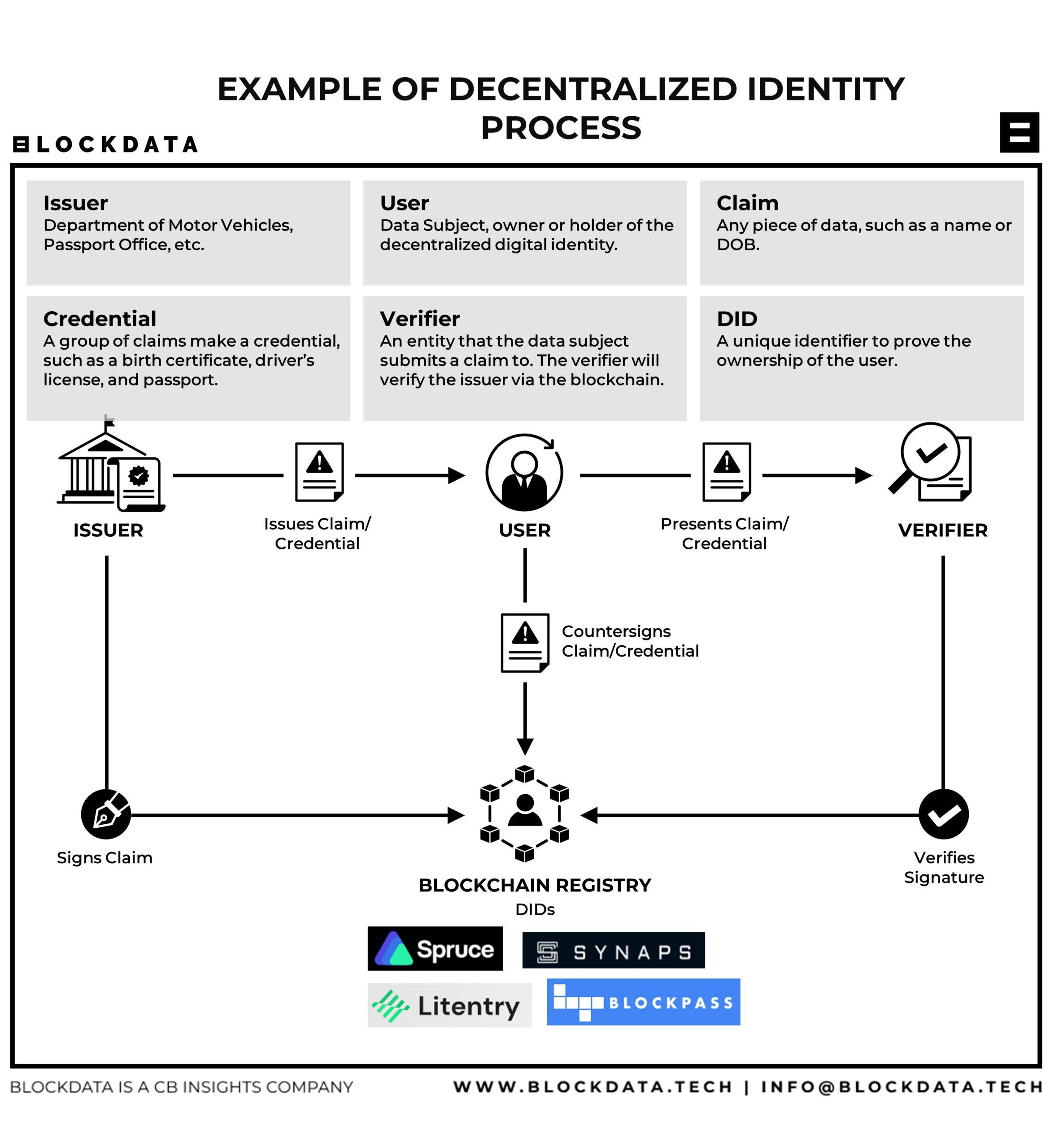
One of the hallmarks of Simplilearn’s approach to education is its emphasis on practical, real-world applications. Rather than focusing solely on theoretical concepts, Simplilearn encourages learners to apply their newfound knowledge to practical scenarios, preparing them for the challenges of the modern workplace. From developing smart contracts to building decentralized applications, Simplilearn empowers learners to translate theory into tangible results.
Expert Guidance: Learning from Industry Leaders
Central to Simplilearn’s success is its team of industry-leading experts who bring years of hands-on experience to the classroom. Through live sessions, interactive discussions, and personalized feedback, learners have the opportunity to engage directly with industry professionals, gaining invaluable insights and guidance along their learning journey. With Simplilearn, you’re not just learning from a textbook—you’re learning from the best in the field.
Flexible Learning: Tailored to Your Schedule
One of the key advantages of Simplilearn Blockchain is its flexibility. Whether you’re a working professional with a busy schedule or a student balancing coursework and extracurricular activities, Simplilearn offers a variety of learning options to suit your needs. From self-paced courses to live online classes, you have the freedom to learn at your own pace, whenever and wherever it’s most convenient for you.
Community Engagement: Fostering Collaboration and Growth
In addition to its expert-led instruction, Simplilearn fosters a vibrant community of learners, where collaboration and knowledge-sharing are encouraged. Through forums, discussion boards, and networking events, learners have the opportunity to connect with like-minded individuals, exchange ideas, and build valuable professional relationships. With Simplilearn, you’re not just gaining knowledge—you’re becoming part of a supportive and dynamic community.
Continuous Learning: Investing in Your Future
In today’s fast-paced world, the need for continuous learning has never been greater. Simplilearn recognizes that the skills needed to succeed in the digital age are constantly evolving, which is why it offers lifelong access to its courses