Ensuring Trust in Decentralized Systems with Secure Consensus Algorithms
In the rapidly evolving landscape of blockchain technology, the security of consensus algorithms plays a pivotal role in maintaining trust within decentralized systems. As the demand for robust and reliable blockchain networks continues to grow, implementing secure consensus algorithms becomes paramount.
Understanding the Foundation: Consensus Algorithms in Blockchain
Consensus algorithms form the backbone of any blockchain network. They determine how nodes within the network agree on the state of the ledger. Commonly used algorithms include Proof of Work (PoW) and Proof of Stake (PoS). Each algorithm has its strengths and weaknesses, and understanding their nuances is crucial for building a secure decentralized system.
The Vulnerabilities of Traditional Consensus Algorithms
While traditional consensus algorithms have proven effective, they are not immune to vulnerabilities. PoW, for instance, faces challenges related to energy consumption and susceptibility to 51% attacks. PoS, on the other hand, may be vulnerable to attacks if a malicious actor amasses a significant amount of cryptocurrency.
Innovations in Secure Consensus Algorithms
To address the limitations of traditional algorithms, the blockchain community has been actively exploring and implementing innovative consensus mechanisms. These newer approaches focus on enhancing security, scalability, and sustainability. Some notable examples include Practical Byzantine Fault Tolerance (PBFT), Delegated Proof of Stake (DPoS), and Hashgraph.
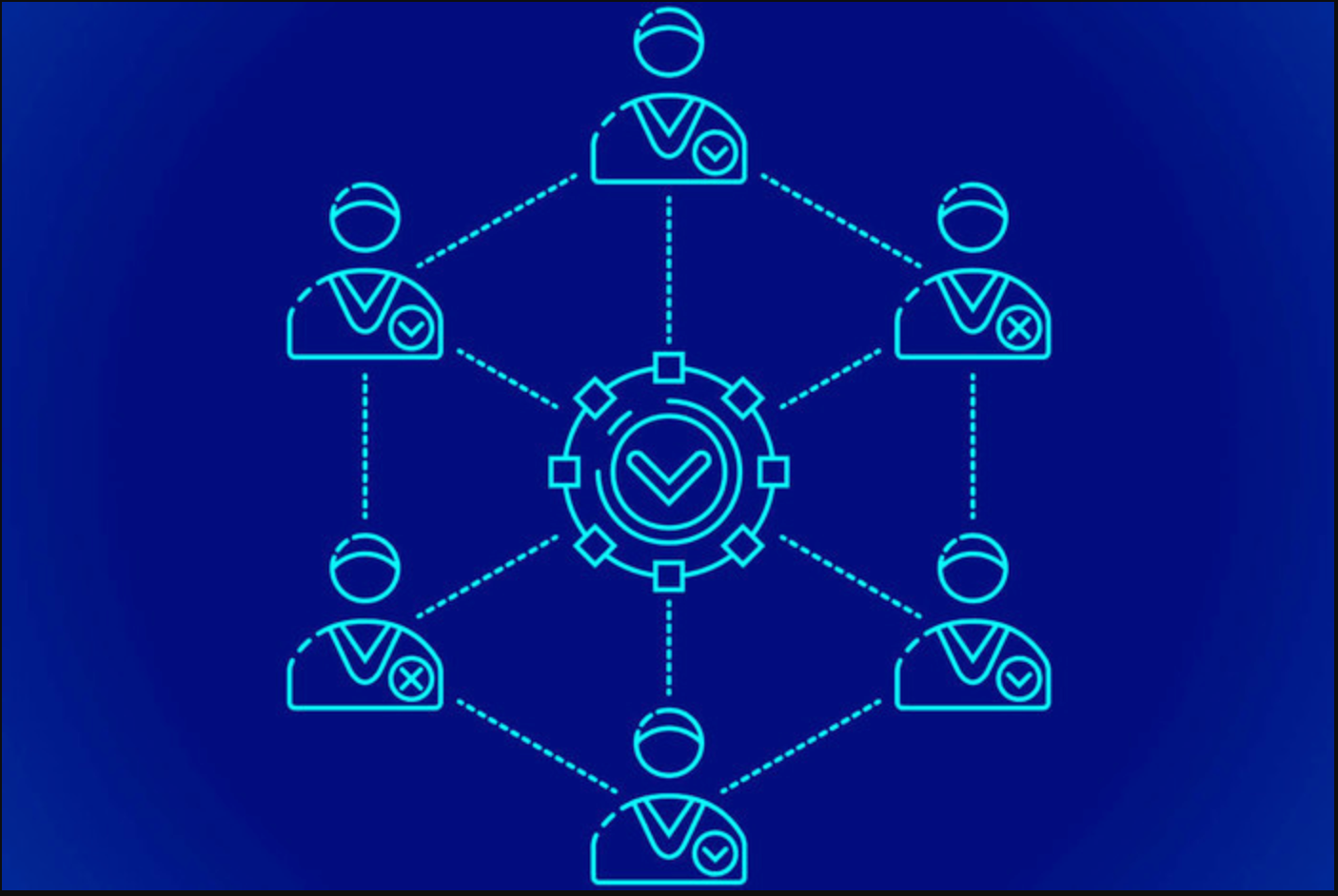
Practical Byzantine Fault Tolerance: Enhancing Security through Agreement
PBFT is a consensus algorithm designed to tolerate Byzantine faults within a network. By ensuring agreement among nodes even in the presence of malicious actors, PBFT significantly enhances the security of decentralized systems. This makes it an attractive option for applications where trust is paramount.
Delegated Proof of Stake: Balancing Power and Security
DPoS introduces a more democratic element to the consensus process. By allowing token holders to vote for a limited number of delegates who validate transactions, DPoS seeks to strike a balance between decentralization and efficiency. This approach addresses some of the scalability concerns associated with PoW and PoS.
Hashgraph: Leveraging Gossip about Gossip for Enhanced Security
Hashgraph is a novel consensus algorithm that leverages a gossip protocol to achieve consensus. By efficiently disseminating information about transactions, Hashgraph aims to provide a high level of security and fairness. Its unique approach positions it as a promising contender for the future of secure consensus mechanisms.
Implementing Secure Consensus Algorithms in Real-World Applications
The adoption of secure consensus algorithms is not confined to theoretical discussions. Real-world applications across industries are actively integrating these mechanisms to ensure the integrity and security of their decentralized systems. From finance to healthcare, the benefits of secure consensus algorithms are becoming increasingly apparent.
Challenges and Future Considerations in Secure Consensus
While secure consensus algorithms offer significant advancements, challenges still exist. Ongoing research and development are necessary to address potential vulnerabilities and ensure the continued evolution of secure consensus mechanisms. As the blockchain ecosystem matures, new challenges and opportunities will undoubtedly emerge.
Secure Consensus Algorithms: A Cornerstone for Trust in Blockchain
In conclusion, the implementation of secure consensus algorithms is a crucial step