Key Encryption: Safeguarding Data with Public and Private Keys Public and private key encryption is a cornerstone of modern cybersecurity,…
Read More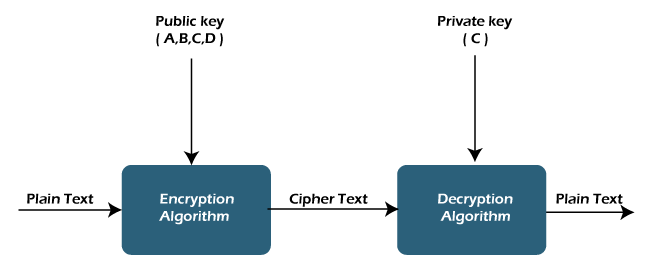
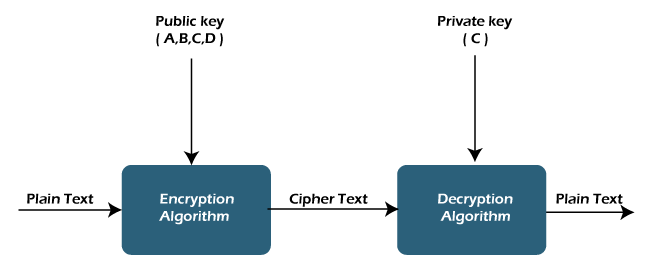
Key Encryption: Safeguarding Data with Public and Private Keys Public and private key encryption is a cornerstone of modern cybersecurity,…
Read More